ACTU
Franchise CBD : Un marché en pleine expansion
Le marché du cannabidiol (CBD) a explosé en popularité au cours des dernières années, attirant l'intérêt des entrepreneurs et investisseurs. Cette croissance rapide est soutenue par un intérêt croissant pour ...
AUTO
ENTREPRISE
LOISIRS
Mythologie japonaise : découvrez les principaux dieux et déesses
Au cœur du Japon ancien, bien avant l'ère des samouraïs et des shoguns, s'étendait un panthéon riche et complexe, peuplé de divinités aux pouvoirs extraordinaires. ...Bougies blanches : Signification et usage dans les rituels
Les bougies blanches sont souvent associées à la pureté et à la spiritualité. Dans de nombreuses traditions, elles jouent un rôle central dans les cérémonies ...Interprétation florale : la fascinante signification de la rose jaune
La rose jaune, avec sa teinte éclatante et chaleureuse, évoque souvent la lumière du soleil et le bonheur. Toutefois, cette fleur est un symbole aux ...Arts contemporains du 21e siècle : tendances et mouvements clés
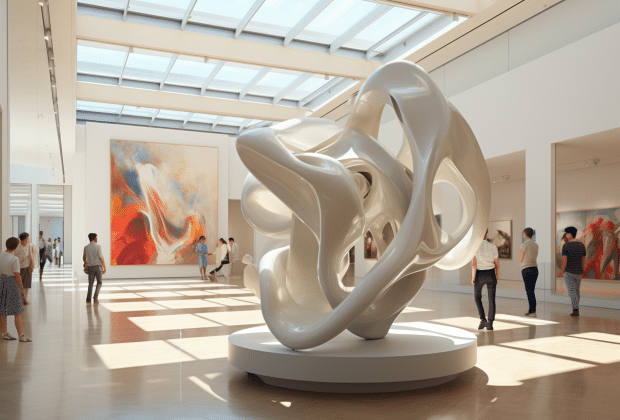
L'art contemporain du 21e siècle est une toile dynamique, constamment en mutation sous l'influence de nouvelles technologies, de préoccupations mondiales et d'un dialogue interculturel sans ...
MODE
Les montres en bois de luxe : une tendance intemporelle pour un style distingué
Dans le monde de l'horlogerie, l'innovation et la tradition se rencontrent souvent pour donner naissance à des tendances à la fois surprenantes et élégantes. Les montres en bois de luxe ...